Mark Baggett of PaulDotCom and I were asked to conduct an insider pentest of a network using 802.1X for port security. Mark was not able to join me during the initial phases of the test, so I was left with the task of figuring out how to bypass the port security so we could attack local targets. As I began to put my plan together, I came up with the following 802.1X attack vectors:
- Use a hub to sniff traffic on the network. Information gathering.
- Spoof an authenticated supplicant off the hub. Allows for passing of UDP and ICMP traffic.
- Write/use a tool which acts as a layer 2 gateway to MitM the authenticated supplicant and ride the 802.1X session.
- If EAP-MD5 is in use, attempt to crack the captured exchange with eapmd5cracker.py and authenticate to the switch.
- Allows for passing TCP traffic.
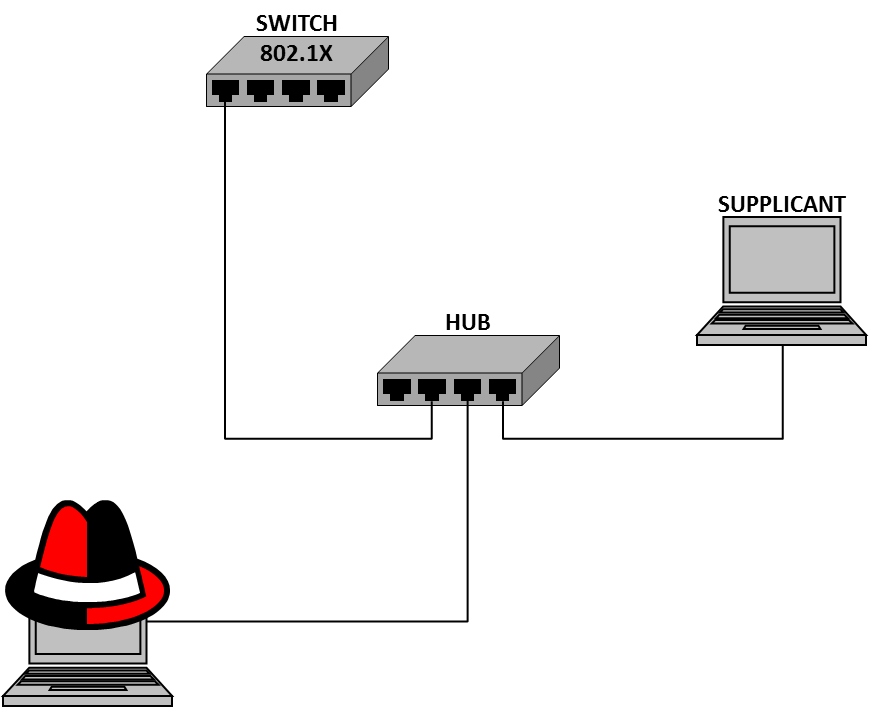
EAP-TLS authentication was in use for the supplicants which were on the segment I wanted access, so vector 3b was not an option at this juncture. Here is what my initial setup looked like:
Once in this configuration, I was able to execute attack vectors 1 and 2. However, the problem with the above configuration is that neither machine can pass TCP traffic while both are connected. When one of the machines sends out a SYN, both receive the SYN/ACK. The machine not expecting the SYN/ACK will send a RST and kill the connection for the other machine. While I realize that unplugging the authenticated supplicant would allow for successful TCP connections, if the switch is forcing 802.1X re-authentication, connectivity would break during the re-auth process. As Red Teamers, we err on the side of transparency, and don't want to take chances creating unnecessary error log entries. Hence, the need for a tool.
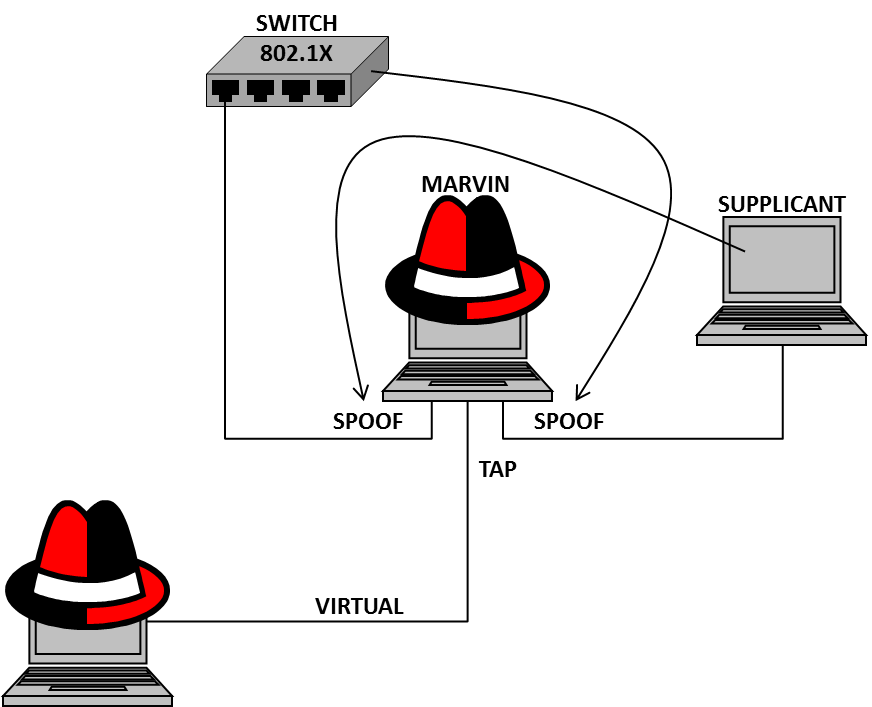
Before dedicating myself to writing a tool to do this, I did some quick research which yielded this. Marvin. A tool written by abb of Gremwell (thanks abb!!) which "diverts and re-injects network connections while preserving the original network addresses, including layer 2." Perfect. My setup for attack vector 3 looked like this:
In order to conduct the attack as passively as possible, I gathered all the necessary configuration information from the network prior to using Marvin. Here's the step-by-step of what I did.
- Put the sniffer interface in promisc mode.
- Sniffed the wire using tcpdump.
- Stored to a pcap file.
- Analyzed with NetworkMiner (thanks carnal0wnage!!).
- Determined all layer 3 and layer 2 information about the network gateway and authenticated supplicant.
- Configured and started Marvin.
- Connected physical adapters (client first to avoid unknown 802.1X auth log entry).
- Connected to tap gateway with my attack platform.
- Hacked away at the internal network.
- VICTORY!

Please share your thoughts, comments, and suggestions via Twitter.
Tweet Follow @lanmaster53